With the ever-changing nature of technology comes the risk of digital attacks and cybercrime. According to
Norton, more than 50% of all consumers have experienced a cybercrime, with around one in three falling victim in the past year alone. The increasing reliance on computers, technology, and data is leaving organizations and individuals more vulnerable than ever to cybercrimes that cause IT and system shutdowns. Considering the consistent and rapid advancement of technologies across industries, it is crucial to be aware of cybercrime methodologies and how to protect oneself against attacks.
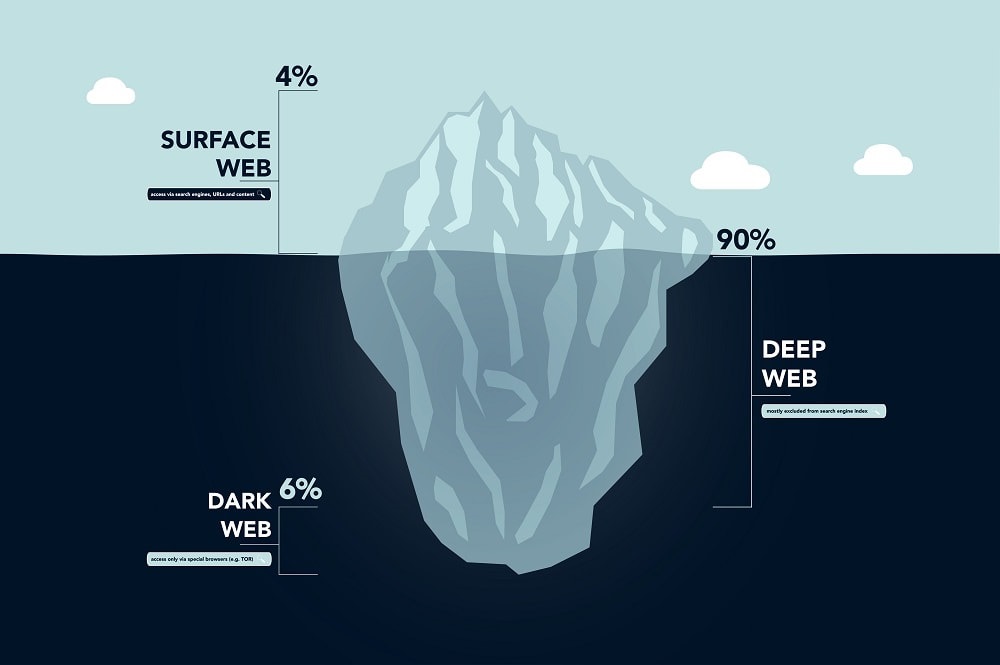
Considering society’s heavy reliance on technology for facilitating business, e-commerce, banking, and communications, it is crucial to disseminate the latest research on how to prevent and manage cyber-attacks. The
Encyclopedia of Criminal Activities and the Deep Web is a three-volume set that provides the most diverse findings and new methodologies for monitoring and regulating the use of online tools as well as hidden areas of the internet, including the deep and dark web. The publication is organized into five separate sections that provide comprehensive coverage of critical topics. The sections include the following:
- Cybercriminal Profiles, Understanding Cybercrime, and the Realities of the Dark Web
- Cyberwarfare, Cybersecurity, Spyware, and Regulatory Policies and Solutions
- Drug Trafficking, Human Trafficking, and the Sexual Exploitation of Children
- Financial Fraud, Identity Theft, and Social Manipulation Through Social Media
- Security Tools and Solutions, Human-Based Cyber Defense, and the Social Understanding of Threats
The encyclopedia offers strategies for the prediction and prevention of online criminal activity and examines methods for safeguarding internet users and their data from being tracked or stalked.
| | Encyclopedia of Criminal Activities and the Deep Web | Mehdi Khosrow-Pour D.B.A. (Information Resources Management Association, USA)
©2020 | 1162 pgs. | EISBN13: 9781522597162 | - Receive 10% Discount on All IGI Global published Book, Chapter, and Article Products through the Online Bookstore
- Suitable for Policy Makers, Law Enforcement Officials, Criminologists, & More
- Covers Topics such as Cyber Abuse, Internet Privacy, & the Dark Web.
- Excellent Addition to Your Institution's Library
|
| |
|
|
According to a
Forbes article written by the Director of the
Quantum Alliance Initiative, Arthur Herman, the United States federal government is taking strides to implement preventative technologies that can predict cyber-attacks before they happen. The Army Analytics Group (AAG) took an offer from the quantum computing and AI company
Entanglement Inc. in June of 2021 to test their proprietary technology. Herman writes, “What does all this mean? Entanglement Inc. is just another indication of a larger truth, i.e. that artificial intelligence and machine learning; blockchain and quantum; are all part of a growing convergence in how we will process and protect data and develop and secure networks in the future. There is, and there will never be, a single technological fix to our cybersecurity woes. Instead, the answer will be a range of hybrid solutions, that draw on the best features of each technology.” One of the five key sections of the Encyclopedia of Criminal Activities and the Deep Web examines artificial intelligence and technology more in depth through the exploration of security tools and solutions, human-based cyber defense, and the social understanding of threats.
"Cyber security transcends technology. To mitigate risk, we need to understand the people behind the technical systems - the targets, the adversaries, and those tasked with protecting those systems. In this book, we explore the psychological and behavioural factors that need to be considered if we are to protect and defend cyber space." — Prof. John McAlaney, Bournemouth University, UK
In more recent news, a New Jersey man was sentenced to nine years in state prison for leading a dark web drug ring that laundered $USD 2.3 million in cryptocurrency. According to
an article published by the Observer, the group manufactured and sold hundreds of thousands of tablets of controlled substances through the dark web and laundered the cryptocurrency by loading prepaid debit cards. Chapter 32 of the Encyclopedia of Criminal Activities and the Deep Web explores how the dark web facilitates illegal drug trafficking through cryptocurrency markets and darknet markets.
Cybercrime has become commonplace not just in the United States, but it affects many nations around the world. According to an
article published by The Guardian, a cyberattack that experts believe has been carried out by Russians has breached the private health data of nearly 10 million Australian citizens. The sensitive information includes records of drug and alcohol treatments, abortions, and mental health issues stored in the databases of Australia’s largest private health insurer, Medibank. After Medibank refused to pay a $USD 9.7 million ransom, the hackers began releasing the patient data on the dark web, leaving millions of individuals at risk with their names, birthdays, addresses, and Medicare numbers stolen. As criminals continue to harness technological advancements that are outpacing legal and ethical standards, law enforcement and government officials are faced with the challenge of devising new and alternative strategies to identify and apprehend criminals to preserve the safety of society.
View Cybersecurity Titles
"Presently, cybersecurity is being seen as an integral part of national security and countries are creating their own "cyber armies" to deal with such attacks. The increasing reliance of commercial businesses and other enterprises on cyber technologies, including interconnected networks and remote access, creates new and expanding vulnerabilities that technically-savvy extremists will exploit - India will not be an exception. Online propaganda that targets Indian interests has become more prevalent since the beginning of 2020. Like in Kashmir, Internet blockades and ‘downgrades’ from 4G to 2G i.e. slower internet access has not been able to stop the extremist propaganda posted by militant groups on Telegram, Twitter, Facebook, WhatsApp, etc. In view of countering 'cyberextremism' and the terror threats posed thereof, initiatives taken up by the Government of India in the last five years include Indian Cyber Crime Coordination Centre (I4C), National Cyber Crime Reporting Portal, Cyber Swachhta Kendra, pushing for Cyber Security Research and Development Centre of India along with National Intelligence Grid (NATGRID) in addition to the National Cyber Security Policy 2013. The modern world cannot be free from cyberspace. Cyberspace is growing every day - India holds a prime position. With broadband traffic increasing day by day, I strongly feel a uniform cyber law at the national and international level is the need of the hour."
There is still much uncertainty around the nature of cyberattacks and the reasoning behind them. Actively working to advance cybersecurity research is crucial to gaining a full understanding of why and how cybercrime occurs, and how innovative solutions can be integrated into systems and processes used by organizations, government institutions, and individual users.
Recommend the Encyclopedia of Criminal Activities and the Deep Web to your institution's librarian today and stay up to date on crucial and timely cybersecurity research.
About IGI Global
Founded in 1988 and headquartered in Hershey, Pennsylvania, USA with a subsidiary office (IGI Science and Technology, Ltd.) operating out of Beijing, China, IGI Global is a leading medium-sized independent international academic publisher of scholarly reference sources. They are committed to facilitating the discovery of pioneering scientific research that enhances and expands the body of knowledge available to the research community through traditional and open access publishing workflows. Working in close collaboration with more than 150,000+ expert researchers and professionals from leading institutions, IGI Global publishes quality peer-reviewed content across 350+ topics in 11 core subject areas, including business, computer science, education, engineering, healthcare, social sciences, and more. Learn more about IGI Global here.
Emma Baronak
(717) 533-8845 ext. 183
ebaronak@igi-global.com
www.igi-global.com